ON THIS PAGE
What Are You Overlooking?
EagleEye365: Eliminate Security Blind Spots.

The Sarbanes-Oxley Act (SOX) was introduced to protect investors by enhancing financial transparency and accuracy. For publicly traded companies, compliance with SOX is essential. IT plays a crucial role in ensuring companies meet SOX’s rigorous internal control standards by safeguarding data integrity, managing access controls, and streamlining compliance processes. With support from SOX Compliance Services, organizations can leverage advanced technological solutions that increase transparency and mitigate financial risks.
The Role of IT in SOX Compliance
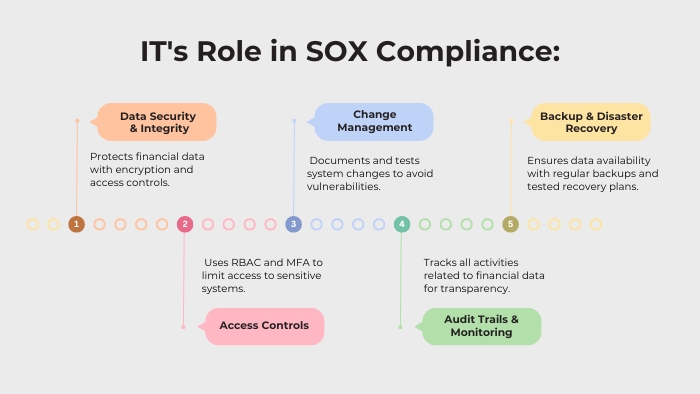
Information Technology is at the core of maintaining SOX compliance, as it directly impacts the security and accuracy of financial data. In today’s digital landscape, where financial reporting relies heavily on technology, IT must ensure that adequate controls are in place to meet SOX requirements. The key areas where IT plays a significant role include:
Data Security and Integrity
IT ensures data security by preventing unauthorized access, breaches, or tampering, and safeguarding sensitive financial information. Strong encryption, access control, and regular system audits protect data integrity across storage, transmission, and processing.
Access Controls
Controlling access to critical financial systems is essential for SOX compliance. IT should implement role-based access control (RBAC) and multi-factor authentication (MFA) to restrict data access to authorized personnel. Regular access reviews and timely removal of permissions for former employees help minimize internal fraud risks.
Change Management
Managing system changes ensures that updates do not compromise SOX compliance. IT is responsible for documenting, testing, and approving any modifications to financial systems, thus safeguarding data integrity and preventing vulnerabilities.
Audit Trails and Monitoring
IT enhances transparency by maintaining comprehensive audit trails that record all activities related to financial data. These logs are essential for detecting unauthorized actions and provide critical evidence during audits.
Backup and Disaster Recovery
Reliable backups and disaster recovery strategies ensure data availability and integrity, especially during system failures or cyberattacks. Regularly tested disaster recovery plans help maintain secure, uninterrupted access to financial data in emergencies.
Best Practices for IT SOX Compliance
IT departments can enhance SOX compliance by adopting the following best practices to strengthen controls and minimize risks.
Automate Controls and Monitoring
Automate critical processes such as access management, change tracking, and audit logging to minimize human error and maintain continuous oversight of financial systems.
Regular Testing of Internal Controls
Perform routine testing of IT controls to confirm compliance with SOX standards. Address any identified promptly to sustain a secure, compliant environment.
Enforce Strict Access Controls
Restrict access to financial systems to authorized personnel only. Conduct regular user permission reviews to prevent unauthorized access.
Maintain Comprehensive Audit Trails
Document all user activity related to financial data with detailed logs. Regularly review these logs to detect and address any unauthorized or suspicious behavior promptly.
Implement Strong Data Security Measures
Protect financial data with proactive security measures such as encryption, firewalls, and real-time threat detection.
Disaster Recovery and Backup Plans
Develop and test robust backup and disaster recovery strategies to minimize disruptions to financial data during system outages or cyberattacks Leverage Governance, Risk, and
Compliance (GRC) Tools
Utilize GRC tools to streamline risk, compliance, and internal control management, giving an organized framework for maintaining SOX compliance.
Conclusion
For effective SOX compliance, IT departments must adopt best practices that reinforce the accuracy, security, and integrity of financial systems. By automating controls, enforcing strict access management, and maintaining strong data security, IT can play a crucial role in supporting SOX requirements. Continuous monitoring and proactive collaboration across departments will further minimize risks, helping organizations remain compliant and enhancing financial transparency.